Quantum Readiness for the Enterprise: Why Preparation Must Start Now
Dec 2025 · Cybersecurity
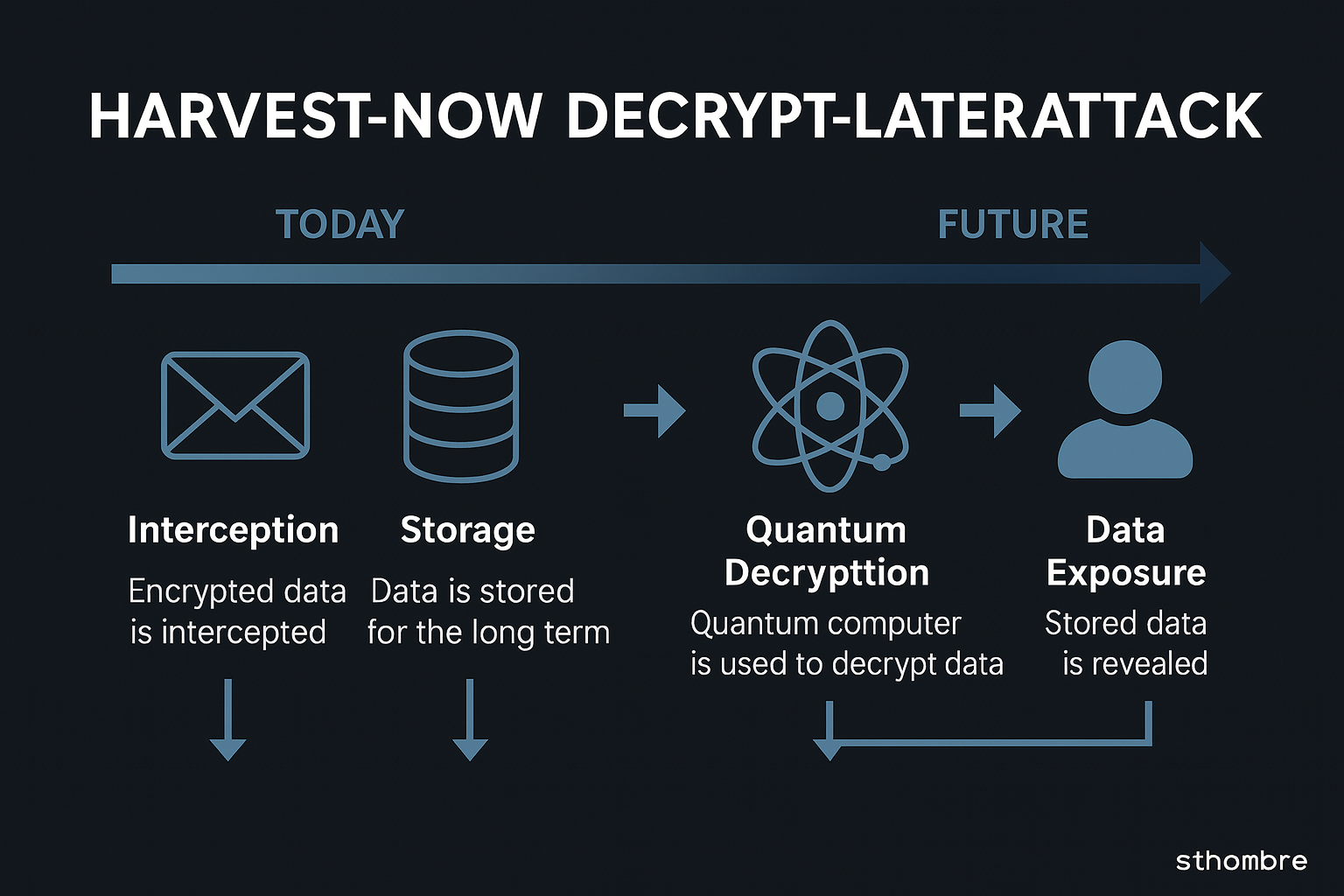
Quantum computing is no longer a distant research milestone. Between government investments, maturing hardware, and major industry breakthroughs, the timeline for quantum-capable systems is shrinking. Even though today's quantum machines cannot yet break RSA or ECC in real time, the threat has already arrived in another form: attackers stealing encrypted data now and waiting until quantum computers can decrypt it.
This is known as a Store-Now, Decrypt-Later (SNDL) attack — and it's becoming one of the most concerning long-term risks in cybersecurity.
Why Quantum Is Already a Real Enterprise Risk
Unlike conventional compute improvements, quantum computing undermines foundational cryptographic assumptions. Algorithms like RSA, ECC, and Diffie–Hellman rely on mathematical hardness problems that a sufficiently large, fault-tolerant quantum computer could solve using Shor's algorithm. Once that threshold is reached, decades of encrypted data become instantly readable.
The urgency comes from a simple reality:
Data often lives far longer than the encryption protecting it.
Long-lived data — healthcare records, intellectual property, M&A files, defense communications, scientific archives, encrypted backups — can stay sensitive for 10–30 years. But the cryptographic algorithms guarding them might not survive even a decade once quantum systems mature.
That creates a dangerous gap: attackers don't need quantum capability today. They only need to capture the ciphertext now and wait.
SNDL Example
A threat actor intercepts a company's encrypted TLS traffic feeding into a cloud data warehouse. They cannot decrypt it today, but they quietly store months of encrypted packets. Years later — once quantum computing advances — the attacker revisits the archive and decrypts every transaction, credential, and sensitive record.
The sting of SNDL is that the breach occurs years before the victim realizes it.
Recent Quantum Breakthrough (Google, 2025)
In October 2025, Google announced a major leap in quantum capability. Its new Quantum Echoes algorithm, running on the "Willow" quantum processor, completed a physics-simulation workload 13,000× faster than a classical supercomputer. This wasn't a laboratory stunt — it was a verifiable demonstration of quantum advantage with practical scientific relevance.
While this does not break encryption, it shows how rapidly quantum hardware is improving. Progress in simulation, error-correction techniques, and qubit stability often leads directly to advances that shrink the time horizon for breaking classical cryptography.
For cybersecurity, this reinforces a key message: the quantum threat timeline is accelerating, not slowing.
NIST's Role: The New Cryptographic Foundation
The National Institute of Standards and Technology (NIST) leads the global transition toward quantum-safe cryptography. After extensive evaluation, NIST selected the first standardized post-quantum algorithms:
- CRYSTALS-Kyber — Key Encapsulation Mechanism (replacement for RSA/ECDH)
- CRYSTALS-Dilithium — Digital Signatures (replacement for RSA/ECDSA)
- Falcon — Alternative digital signature scheme
- SPHINCS+ — Hash-based signatures
NIST has also published critical guidance, including:
- NIST SP 800-208 — Hybrid classical + PQC deployments
- Migration frameworks for federal agencies and critical infrastructure
- Requirements to inventory all cryptographic assets and transition to PQC
For enterprises, NIST's PQC suite is now the de facto global standard.
How Enterprises Should Prepare (Practical Steps)
Quantum readiness is a multi-year transformation because cryptography is deeply embedded across networks, applications, hardware, and supply chains. Key steps include:
1. Build a Cryptographic Inventory
Most organizations don't actually know:
- which algorithms they use
- where cryptographic keys live
- which systems depend on RSA/ECC
- what data has long-term confidentiality needs
This foundational visibility is the hardest — and most essential — step.
2. Identify Quantum-Vulnerable Systems
High-risk components typically include:
- TLS termination and load balancers
- VPN gateways
- PKI roots, intermediates, and certificate lifecycles
- Encrypted backups and archives
- S/MIME / PGP email systems
- Identity and access systems
- IoT or embedded devices that may not be upgradeable
3. Implement Crypto-Agility
Enterprises must be able to swap cryptographic algorithms without redesigning systems. This means:
- abstraction layers around crypto libraries
- removing hardcoded primitives
- enabling PQC-capable certificate structures
- adopting flexible key-management architectures
4. Begin Pilot Deployments of PQC (Hybrid Mode)
Start with controlled rollouts in:
- internal PKI
- TLS gateways using hybrid KEMs (e.g., X25519 + Kyber)
- code-signing systems
- firmware or secure update mechanisms
Hybrid mode provides resilience while PQC standards stabilize.
5. Integrate Quantum Risk Into Governance
Quantum readiness must be reflected in:
- enterprise risk registers
- compliance frameworks
- vendor onboarding requirements
- incident-response playbooks
- long-term data retention and archival policies
If third-party vendors are not quantum-ready, your environment isn't either.
6. Track Advances in Quantum Hardware
Breakthroughs in error-correction or qubit stability could dramatically shift timelines. Enterprises should maintain ongoing intelligence on quantum research, industry announcements, and government standards.
Conclusion
Quantum computing does not need to break RSA today to threaten enterprises. The real risk is the silent harvesting of encrypted data that will be decrypted years in the future. Google's 2025 breakthrough underscores that the quantum timeline is compressing. Organizations must begin deep cryptographic inventories, adopt crypto-agility, and plan for migration to NIST-approved PQC.
Quantum readiness isn't about predicting the exact year quantum machines break encryption — it's about ensuring your data remains secure no matter when that day arrives.
Sources
- Reuters — Google says it has developed landmark quantum computing algorithm (2025)
- The Guardian — Google hails breakthrough as quantum computer surpasses supercomputers (2025)
- NIST — Post-Quantum Cryptography Standardization Project
- NIST SP 800-208 — Recommendation for Stateful Hash-Based Signatures
- White House NSM-10: Promoting U.S. Leadership in Quantum Computing
- ENISA — Migration Toward Post-Quantum Cryptography
- NSA — Quantum-Resistant Algorithm Guidance